Download Tor Browser For Mac
Posted : admin On 19.02.2020Running Tor on OpenBSD These are installation instructions for running Tor Browser in a OpenBSD environment. To install from OpenBSD's packages, run: pkgadd tor-browser Sometimes the most recent version of Tor Browser on OpenBSD is behind the current release. The available version of TB on OpenBSD should be checked with: pkginfo -Q tor-browser If provided version is not the current Tor Browser version, it is not recommended. To install the Tor Browser port from an updated ports tree, run: cd /usr/ports/meta/tor-browser && make install. You need to change some of your habits, as some things won't work exactly as you are used to. Use Tor Browser Tor does not protect all of your computer's Internet traffic when you run it. Hope for macky. Tor only protects your applications that are properly configured to send their Internet traffic through Tor.
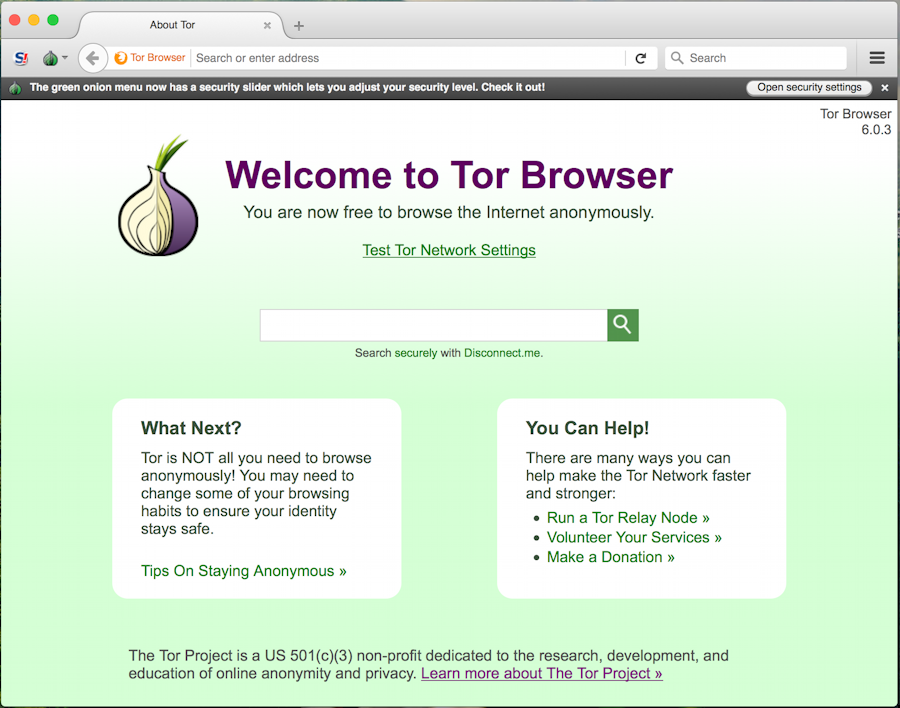
To avoid problems with Tor configuration, we strongly recommend you use the. It is pre-configured to protect your privacy and anonymity on the web as long as you're browsing with Tor Browser itself. Almost any other web browser configuration is likely to be unsafe to use with Tor.
Don't torrent over Tor Torrent file-sharing applications have been observed to ignore proxy settings and make direct connections even when they are told to use Tor. Even if your torrent application connects only through Tor, you will often send out your real IP address in the tracker GET request, because that's how torrents work. Not only do you this way, you also slow down the entire Tor network for everyone else. Don't enable or install browser plugins Tor Browser will block browser plugins such as Flash, RealPlayer, Quicktime, and others: they can be manipulated into revealing your IP address. Similarly, we do not recommend installing additional addons or plugins into Tor Browser, as these may bypass Tor or otherwise harm your anonymity and privacy. Use HTTPS versions of websites Tor will encrypt your traffic, but the encryption of your traffic to the final destination website depends upon on that website. To help ensure private encryption to websites, Tor Browser includes to force the use of HTTPS encryption with major websites that support it.
However, you should still watch the browser URL bar to ensure that websites you provide sensitive information to display a, include in the URL, and display the proper expected name for the website. Also see EFF's interactive page explaining. Don't open documents downloaded through Tor while online Tor Browser will warn you before automatically opening documents that are handled by external applications.
DO NOT IGNORE THIS WARNING. You should be very careful when downloading documents via Tor (especially DOC and PDF files, unless you use the PDF viewer that's built into Tor Browser) as these documents can contain Internet resources that will be downloaded outside of Tor by the application that opens them.
This will reveal your non-Tor IP address. If you must work with DOC and/or PDF files, we strongly recommend either using a disconnected computer, downloading the free and using it with a with networking disabled, or using. Under no circumstances is it safe to use together, however. Use bridges and/or find company Tor tries to prevent attackers from learning what destination websites you connect to. However, by default, it does not prevent somebody watching your Internet traffic from learning that you're using Tor. If this matters to you, you can reduce this risk by configuring Tor to use a rather than connecting directly to the public Tor network. Ultimately the best protection is a social approach: the more Tor users there are near you and the more their interests, the less dangerous it will be that you are one of them.
Convince other people to use Tor, too! Be smart and learn more.
Understand what Tor does and does not offer. This list of pitfalls isn't complete, and we need your help. In some countries the Tor Project website is blocked or censored and it is not possible to download Tor directly.
The Tor Project hosts a Tor Browser. Using the service is another way to download Tor Browser when the Project website and mirrors are blocked.
Why we need Tor Utilizing Tor shields you versus an usual form of Net security called “website traffic evaluation.” Traffic analysis can be used to presume that is speaking to whom over a public network. Understanding the resource and also location of your Net web traffic allows others to track your habits and interests. This could influence your checkbook if, for instance, a shopping site uses rate discrimination based upon your country or establishment of beginning. It can also endanger your task and also physical safety and security by exposing who as well as where you are.
As an example, if you’re taking a trip abroad and you link to your company’s computer systems to check or send mail, you can unintentionally reveal your national origin and also professional affiliation to any person observing the network, even if the link is encrypted. Read Also: Covert solutions additionally makes it possible for individuals to hide their areas while offering various type of solutions, such as web publishing or an immediate messaging server. Making use of Tor “affair points,” other Tor individuals can link to these concealed services, each without understanding the various other’s network identity.
This concealed service performance can enable Tor users to establish a website where people publish material without fretting about censorship. Nobody would be able to identify that was supplying the site, as well as nobody who used the website would certainly recognize that was uploading to it. Find out more regarding configuring hidden solutions and also just how the covert solution procedure functions. Read Also: Staying confidential Tor Browser 7.0.5 cannot address all privacy problems.
Tor Browser Mac Os X
It focuses only on securing the transportation of data. You need to use protocol-specific assistance software program if you don’t want the websites you visit to see your identifying information. For instance, you could use Tor Browser while searching the web to hold back some information concerning your computer’s setup. Requirements: Windows XP / Vista / Windows 7 / Windows 8 / Windows 8.1 / Windows 10/ Mac OS Latest Version: Tor Browser 7.0.5 Name: Tor Browser Sizi: 50.97MB Download Tor Browser 7.0.5 Latest Version Supported versions Download Tor Browser 7.0.5 For Windows XP / Vista / Windows 7 Tor Browser 7.0.5 For Windows 8 / Windows 8.1 / Windows 10/ Tor Browser 7.0.5 For Windows Mac.